The Ultimate Guide to Crypto Wallets: Everything You Need to Know and More
Apr 4, 2023
Jan Hetfleiš
Welcome to our comprehensive guide to the world of crypto wallets. In this article, we'll dive into the fascinating topic of crypto wallets from multiple angles. We'll examine the different types of wallets available, exploring their various features and functions. We'll also address key questions such as how crypto wallets generate revenue, and provide you with practical tips for using them safely and effectively. Finally, we'll take a look at the future of crypto wallets and offer our perspective on what lies ahead. So let's get started from the beginning!
What is a crypto wallet?
Cryptocurrency wallets store users' public and private keys, while providing an easy-to-use interface for managing digital assets. They also support cryptocurrency transfers via the blockchain. Some wallets even allow users to perform certain actions with their digital assets, such as buying and selling or interacting with decentralized applications.
It is important to remember that cryptocurrency transactions do not involve 'sending' digital assets from one person's mobile phone to another person's mobile phone. When digital assets are sent, a user's private key signs the transaction and sends it to the blockchain network. The network then incorporates the transaction to reflect the updated balance in both the sender's and recipient's address.
The term 'wallet' is therefore somewhat misleading, as crypto wallets don't actually store cryptocurrency in the same way that physical wallets store cash. Instead, they read the public ledger to show a user's balances, and hold the private keys that allow the user to make transactions.
As mentioned above, wallets store two types of keys.
Public key
A public key allows users to receive cryptocurrency transactions. It is public and available to everyone in the system.
Private key
A user's private key proves ownership of their respective public key. It must be stored separately and kept secret. In simple terms, it can be thought of as a password to a bank account.
Wallet address
There is one more thing about public keys. It is sometimes misinterpreted as a wallet address, but wallet addresses are essentially hashed versions of the public key. Public keys are compressed and shortened to make it easier to send an address.
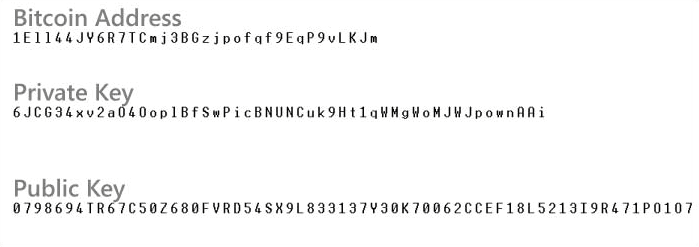
Example of what keys and address looks like
Crypto wallets fall into several categories. There are 3 main categories that we will talk about in this article.
Hot and cold wallets
Custodial and non-custodial wallets
Types of wallets based on their medium
1. Hot and Cold Wallets
The main difference between hot and cold wallets is whether they are connected to the internet. Hot wallets are connected to the internet, while cold wallets are kept offline. This means that funds stored in hot wallets are more accessible and therefore easier for hackers to access.
Types of cold wallets:
Hardware wallets
Paper wallets
Types of hot wallets:
Browser wallets
Browser Extension Wallets
Mobile Wallets
Desktop Wallets
Cold wallets are great because of their portability, they are often small, plug-in devices that can be carried around. They are also the most secure type of wallet. One of the drawbacks is the price. They usually cost between $79 (Trezor Model One) and $316 (Ledger Stax). They're also less convenient for transfers, so the best use for them is to keep safe assets that you don't need to access often.
Hot wallets are generally easy to use because they are connected to the internet, so you can easily access your assets from anywhere. Most are also free to use. Security is the main concern with hot wallets as they can be vulnerable to hacking.
2. Custodial and non-custodial wallets
Custodial
These types of wallets are typically offered on centralised cryptocurrency exchanges such as Kraken, Crypto.com and others. They are convenient and easy to use, and are particularly popular with newcomers.
The main thing about custodial wallets is that users do not have full control over their digital assets and the private key needed to sign transactions. They are only held by the exchange or other custodian.
With a wave of centralised exchange scandals, most recently FTX, people are less willing to keep their digital assets in custodial wallets because there is no guarantee they will not lose them. There is a common saying about this - not your keys, not your crypto.
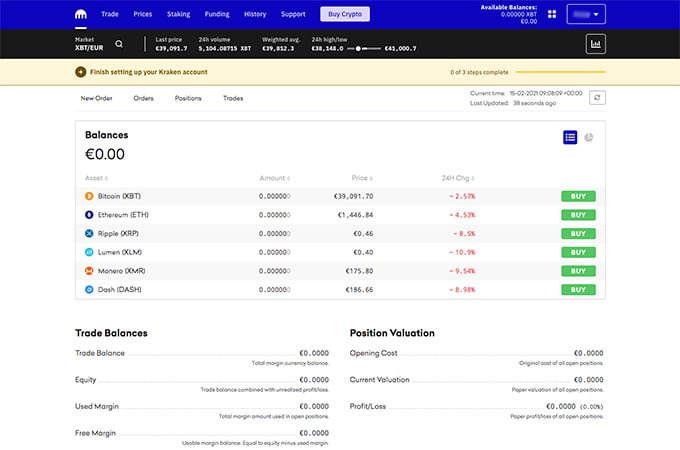
Kraken - custodial wallet
Non-custodial
Non-custodial wallets, on the other hand, allow a user to retain full control of their digital assets because the private key is stored locally with the user.
When starting a non-custodial wallet, the user is asked to write down and securely store a list of 12 or 24 randomly generated words, known as a "recovery", "seed" or "mnemonic" phrase. This phrase can be used to generate the user's public and private keys. This acts as a backup or recovery mechanism should the user lose access to their device.
3. Types of wallets based on their medium
Hardware Wallets
A hardware wallet, often a small plug-in device, is a portable key to securely access your crypto assets from anywhere.
Hardware wallets are considered cold wallets because they isolate your private keys from the Internet, reducing the risk of your assets being compromised in an online attack.
Private keys stored on the hardware wallet are protected by a PIN and optional passphrase. If someone steals your hardware wallet, it's almost impossible for them to extract the keys. The keys are never exposed to the Internet, so they can't be stolen.
If the hardware wallet is lost, the assets are secured with a single seed phrase. A seed phrase, also known as a recovery phrase, is a list of words that will regenerate your private key. The seed phrase can be used to move keys to another hardware wallet.
Most hardware wallets use a protected microcontroller where the chip that connects to the Internet is separate from the chip that stores the private key on the device.
They allow transactions to be physically and manually signed and verified while offline. Physical buttons or touchscreens allow the PIN to be entered, while the on-screen display allows the user to confirm that the address is exactly as desired.
Most have additional security methods such as PIN lock, 2-factor authentication, biometric security and other security procedures.
The most trusted hardware wallets are made by Ledger and Trezor.

Ledger Stax
Browser Wallets
Browser wallets are built directly into the browser. The main advantage over browser extension wallets is that they are less vulnerable to fake versions of an app, phishing and theft.
Browser wallets are currently offered by Brave, Opera and we understand that Microsoft Edge is working on one.
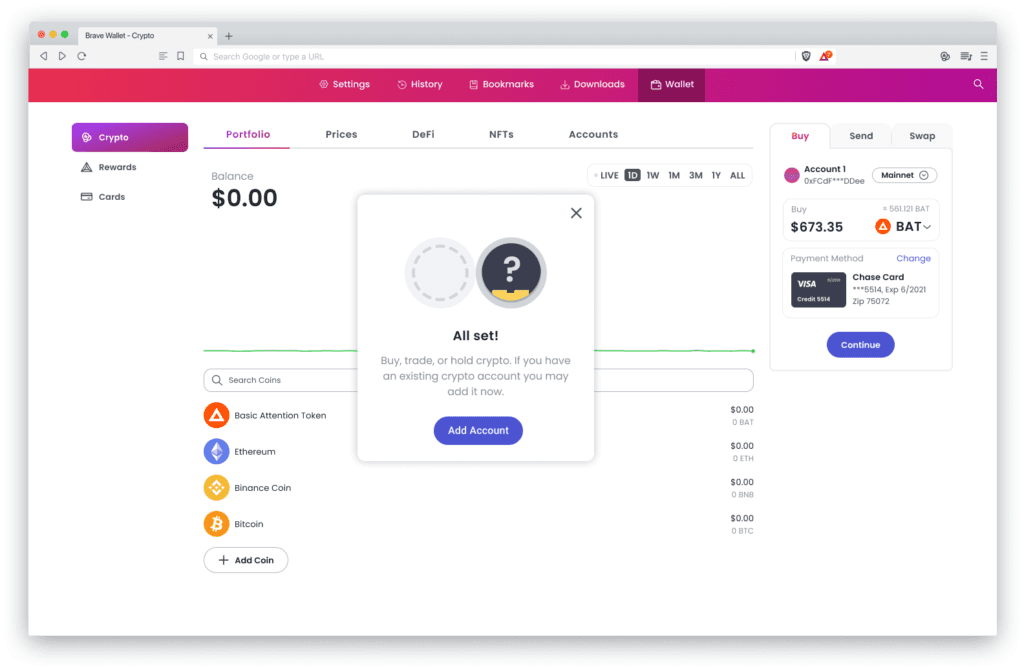
Brave Browser Wallet
Browser Extension Wallets
These are browser extensions that you can access using a supported browser such as Chrome, Brave or Opera. The software runs on the browser as a non-custodial wallet, with all your information stored there. Browser extension wallets are usually built for specific blockchains, but there are a few browser extension wallets that support multiple chains (Coinbase, Zerion, Backpack).
Browser extension wallets are excellent for interacting with decentralized applications, decentralized exchanges, NFTs and other decentralized applications.
There are probably the most wallets in this category. To name just a few:
Metamask
Trust
Argent
Coinbase
Phantom
Backpack
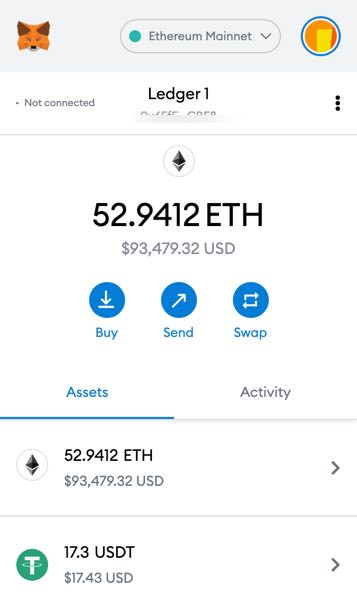
Metamask Browser Extension
Desktop Wallets
Desktop wallets are computer programs that run on a PC or laptop.
They store and manage private keys just like any other wallet, but they often have a few more features than you'll find in other types of wallets.
Each desktop wallet has a different set of features and functions.
Examples of desktop wallets include Exodus or Atomic Wallet.
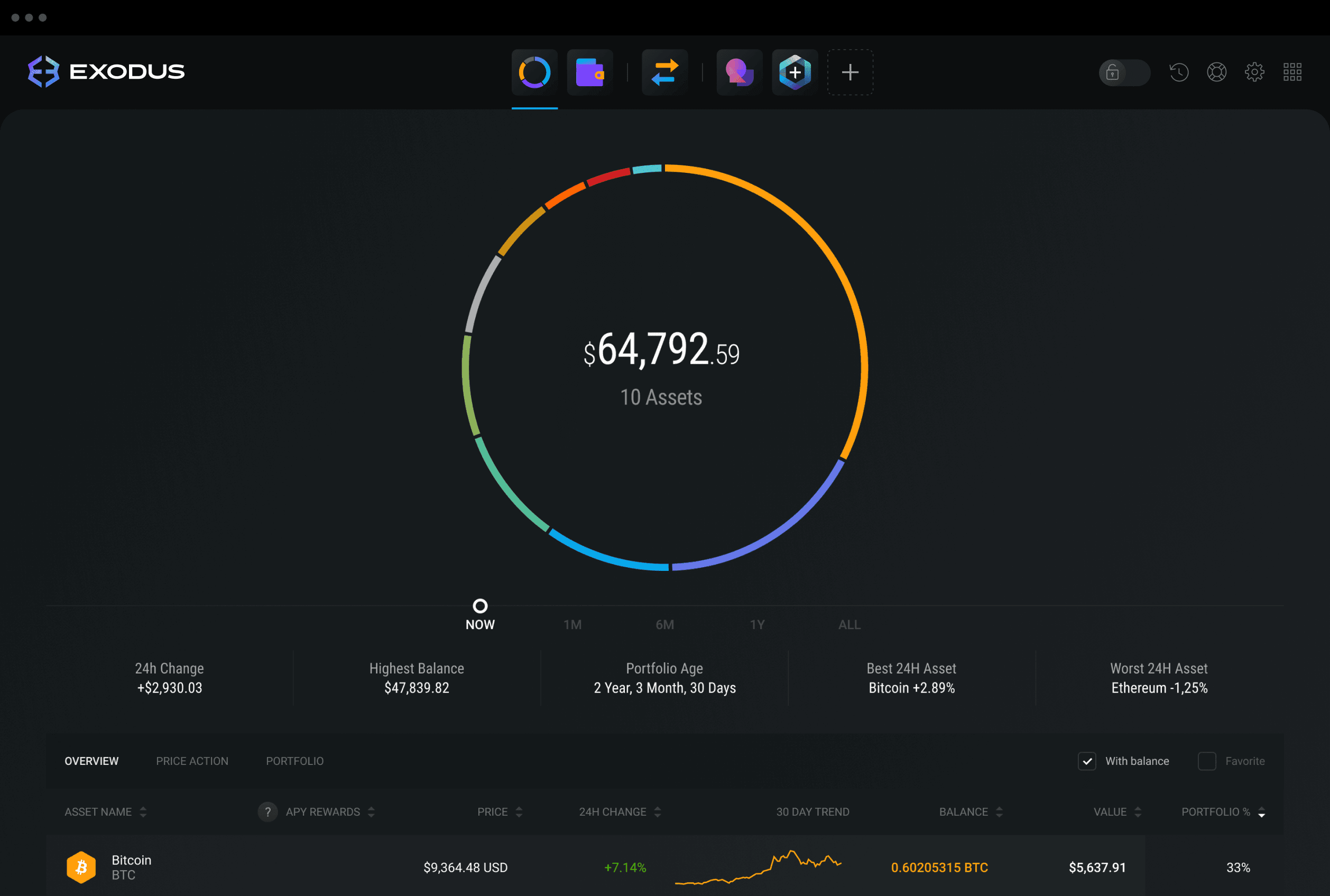
Exodus Desktop Wallet
Mobile Wallets
Mobile crypto wallets are software programs that secure users' funds and allow them to interact with their crypto holdings using their mobile phone or other internet-connected mobile device.
The main benefit of a mobile wallet is the convenience of taking your crypto spending power with you wherever you go. The apps are generally user-friendly and make it easy to buy, store, exchange, spend or otherwise manage digital assets from a mobile device.
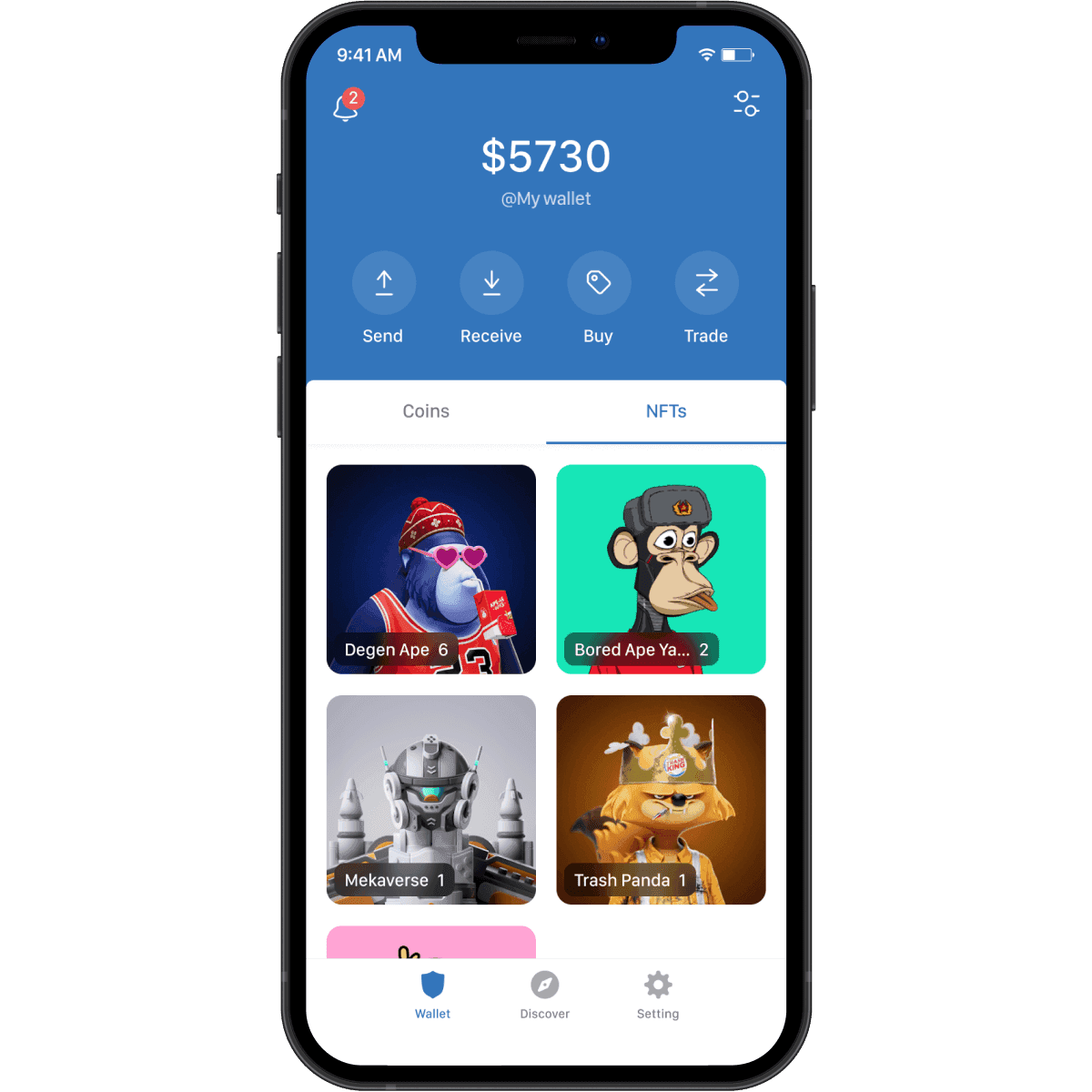
Trust Mobile Wallet
Wallet Functions
1. Send, buy, exchange
Sending and receiving digital assets is a key feature of crypto wallets. Unlike traditional fiat currencies, you can send crypto to anyone, anywhere in the world.
Most wallets also allow you to buy crypto from their partners. This makes it easy to get new users up and running. They also allow you to exchange tokens for others.
2. Multiple accounts
Most wallets offer the flexibility to add multiple accounts. This can be useful for managing different activities such as crypto trading, NFT trading and DeFi investments.
3. Staking and contributing to liquidity pools
Staking allows you to passively earn rewards for holding crypto assets. A liquidity pool is a collection of crowdsourced cryptocurrency or tokens from which people can lend cryptocurrency and liquidity providers are rewarded for doing so. Some wallets allow you to participate in staking and contribute to liquidity pools directly within the wallet.
How Are Wallets Monetized?
You may be wondering how crypto wallets make money. And no, they do not take a cut of the transactions you make.
Most wallets run on affiliates. Because they attract a lot of users and usage, they are able to offer all sorts of features that are nothing more than a way to generate an affiliate commission from third-party services.
The most popular would be the ability to buy or exchange cryptocurrency.
Wallet Best Practices
Use 3 types of wallets
The most basic wallet best practice is to use 3 types of wallets. Hot, cold and what we like to call the YOLO wallet.
If you have more than $1000 in digital assets it is good practice to invest in a hardware (cold wallet). Use a separate hot wallet for daily use with trusted applications and exchanges. If you want to try something new and aren't 100% sure of the security, use the YOLO wallet (another hot wallet), which holds nothing of value and only a small amount of crypto that you can afford to lose.
Secure your seed phrase
Store your seed safely and only physically. Somewhere on a piece of paper that you keep at home. The next level is to engrave your seed into a metal plate, which will protect you in the event of a fire. There are even more advanced measures, such as splitting the seed in half and storing it in a couple of safes in two different places. Under no circumstances should you store the seed virtually, online, on a screen or written on a PC, as you could be hacked and lose everything.
More tips
Don't search for protocols and projects on Google. Often the first ones you see are a scam pretending to be an official projects. Always go through official social networks. Always check the URL.
Don't click on links sent to you by strangers. Be vigilant, don't trust anyone and consider everything a risk until you have verified it in some way.
Use Chrome extensions like Pocket Universe and the like. Even a simple gasless signature can mean that you activate a private sale of all your NFTs for 0 ETH to a scammer.
The Future of Wallets
There are a number of things that can be improved within the wallets, and we believe they will be in the future.
Better seed phrase protection
In the future, there should be better protection of seed phrases. For example, we can see seed phrases being automatically backed up to iCloud when a wallet is created. Another thing is seed recovery. At the moment there is no way to recover seeds, but this will be changed in the future. There has been a new standard ERC-4337 introduced on Ethereum that allows account abstraction and will give wallets similar functionality to bank accounts.
Wallet addresses
At the moment, wallet addresses are a bit clunky. They are not as easy to use as email. There are options to buy ENS or unstoppable domains that you can assign to your wallet and then you can send cryptocurrency to cleevio.eth instead of 0x..... The problem is that domains have an expiration date and you have to remember to renew them. Wallets could help with this.
Better user experience
The signing transaction is a big mess right now. 99% of people don't know what they're signing because transactions look like code. We need wallets to translate transactions for us so we can be informed, be safe and make better decisions.
Another thing is interactions with DeFi protocols. We imagine that in the future, if we put cryptocurrency into a liquidity pool, for example, the wallet will tell us how much we have there and how much we are earning from it.
Phone as a hardware wallet
In the future, phones could act as hardware wallets. At the hardware level. It would be a lot more convenient. We don't see anybody thinking about it now, Google or Apple are not embracing this technology fast enough. It will probably be someone in the crypto industry who develops such a phone first.
Notifications and messages
The last feature we are missing in the wallets is notifications and messages. There are a few wallets that offer notifications, but it is far from perfect at the moment. It would be very convenient if we could get notifications about price changes, eligibility for airdrops and so on. We could also see the benefits of sending messages between wallets. Of course, there is a risk of spam and phishing attacks, so this system has to be very well thought out.
As we close this guide, it's clear that the world of crypto wallets is still in its infancy, with new developments and innovations emerging all the time. It remains to be seen whether a single dominant wallet will emerge, or whether users will continue to use multiple wallets for different purposes. What is certain, however, is that the future of crypto wallets is bright and there are exciting developments on the horizon. We hope this guide has provided you with a solid foundation of knowledge to help you navigate the ever-evolving landscape of crypto wallets.
Building successful
products.together.
© 2008—2023 Cleevio
Lesnicka 1802/11
613 00 Brno
Mississippi House
Karolinska 706/3
186 00 Prague
Prague office
Brno office
CIN 18008844

